Cloud Computing: Federal Agencies Face Four Challenges
Fast Facts
Federal agencies plan to spend billions of dollars each year to support their IT and cybersecurity efforts. These efforts include transitioning their IT resources to secure, cost-effective commercial cloud services.
We've identified challenges in 4 areas that agencies must overcome to fully realize the benefits of transitioning to cloud services. Specifically, agencies face challenges in:
- Ensuring cybersecurity
- Procuring cloud services
- Maintaining a skilled workforce
- Tracking costs and savings
This snapshot discusses our work in this area and recommendations that can help agencies with this transition.

Highlights
As the federal government transitions to cloud computing, agencies face challenges in four areas: ensuring cybersecurity, procuring cloud services, maintaining a skilled workforce, and tracking costs and savings. Our work in these areas—and the implementation of our recommendations—can help agencies overcome these challenges
The Big Picture
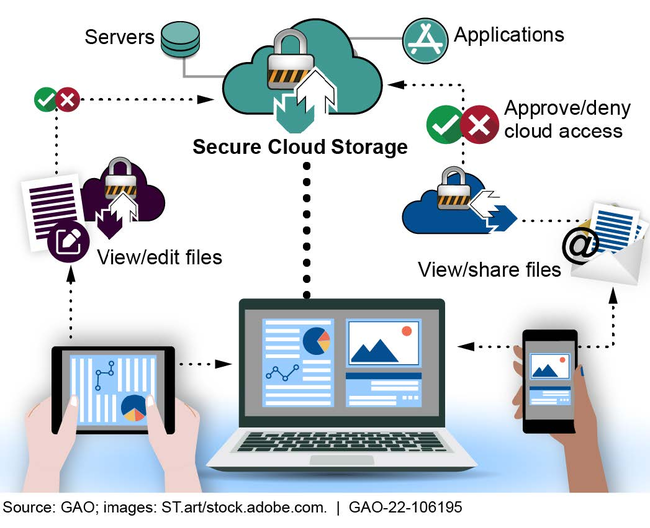
Federal agencies plan to spend billions of dollars each year to support their IT and cybersecurity efforts, including transitioning IT resources to secure, cost-effective commercial cloud services. Federal agencies can use cloud computing to access IT resources—such as servers that store digital files—through the Internet faster and for less money than it would take to own and maintain such resources.
Illustration of a cloud computing environment
What GAO's Work Shows
Our body of work highlights four main challenges related to the federal government’s adoption of cloud services and our recommendations for improvement. Federal agencies have not fully implemented all of the recommendations.
1. Ensuring Cybersecurity
In 2011, the Office of Management and Budget (OMB) established the Federal Risk and Authorization Management Program (FedRAMP) to provide a standardized approach for selecting and authorizing the use of cloud services that meet federal security requirements.
In December 2019, we reported that, while all 24 major federal agencies were participating in FedRAMP, many of these agencies continued to use cloud services that were not authorized through the program. In addition, the four major agencies we selected for a detailed review did not always:
- include required information in their cloud system’s security plans;
- summarize security control test results in security assessment reports; and
- identify required information in remedial action plans that are to list cloud service deficiencies and how they will be mitigated.
We found that one cause of these weaknesses was that FedRAMP’s requirements and guidance on implementing these control activities were not always clear and the program’s process for monitoring the status of security controls over cloud services was limited.
We recommended that OMB hold agencies accountable for authorizing cloud services through FedRAMP. We made an additional 24 recommendations to federal agencies related to improving the implementation of the FedRAMP program, including clarifying guidance on program requirements and responsibilities.
2. Procuring Cloud Services
An important part of procuring cloud services is incorporating a service level agreement into the contract. These agreements define the level of service and performance that the agency expects the contractor to meet. In April 2016, we reported that five of the major agencies that we selected for review did not always incorporate key practices for these agreements in their cloud service contracts. For example, the agencies did not always specify:
- what constitutes a security breach and the responsibilities for notifying the agency;
- how data and networks will be managed; and
- the range of enforceable consequences for non-compliance with the agreement.
This was primarily due to the lack of guidance that fully addressed the key practices.
We recommended that four of the agencies develop guidance that fully incorporates the key practices and that the fifth agency update its guidance to include all of the key practices.
3. Maintaining a Skilled Workforce
Having skilled IT personnel is key to supporting the federal government’s cloud adoption efforts.
Illustration of a cloud computing workforce

Nonetheless, we reported cloud-related workforce challenges at three federal agencies.
- The Coast Guard did not include new cloud-related skills and a skills gap analysis for cloud personnel in its workforce development strategy.
- The Department of Defense (DOD) did not strategically plan for communicating with employees to prepare them for changes that would occur due to the move to cloud services.
- The Department of State’s strategic plan did not include performance measures, targets, or goals to monitor progress towards clarifying job responsibilities and requirements needed to support the cloud environment.
We recommended that the Coast Guard, DOD, and the Department of State take actions by updating their strategic plans to address the workforce issues related to cloud computing.
4. Tracking Costs and Savings
Federal policies and guidance have stressed the importance of reducing acquisition and operating costs by purchasing cloud services through the adoption of cloud computing. However, in April 2019, we reported that federal agencies experienced challenges in tracking and reporting cloud spending and savings data. For example, federal agencies were often using inconsistent data to calculate cloud spending and were not clear about the costs they were required to track. In addition, agencies had difficulty in systematically tracking savings data and expressed that OMB guidance did not require them to explicitly report savings from cloud implementations. We reported that, as a result, it is likely that agency-reported cloud spending and savings figures are inaccurate.
We recommended that OMB require agencies to explicitly report cloud savings, and that agencies establish a repeatable mechanism to track cloud savings and avoidances.
More from GAO’s IT Portfolio
For more information, contact Jennifer R. Franks at (404) 679-1831 or franksj@gao.gov.
