Coast Guard: Actions Needed to Enhance IT Program Implementation
Fast Facts
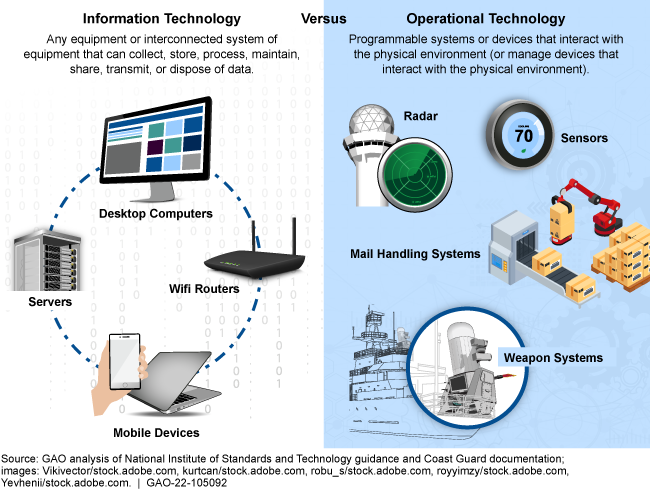
IT systems and operational technology—like sensors and radar—are critical for U.S. Coast Guard operations. However, Coast Guard has a long history of problems managing these resources.
The Coast Guard plans to spend $93 million in fiscal year 2022 to improve its IT systems and infrastructure. But the Coast Guard still doesn't fully assess its IT network capacity needs. For example, it doesn't test bandwidth limits to know when busy network traffic may affect performance. Also, Coast Guard doesn't include all of its operational tech in its cybersecurity efforts.
We made 8 recommendations to the Coast Guard addressing these and other issues.
Common Types of Information Technology and Operational Technology
Highlights
What GAO Found
The U.S. Coast Guard lacks a documented network capacity planning process. Network capacity planning is an important aspect of IT infrastructure planning that involves determining the network resources required to support an entity's mission. However, the Coast Guard uses an ad hoc process that does not fully align with five common practices GAO identified for network capacity. The table below describes the extent to which it implemented the practices. Without fully implementing these practices, the Coast Guard faces significant risks in resulting inefficiencies and disruptions in network availability to users.
Extent to Which Coast Guard Implemented Network Capacity Planning Practices
|
Common Practices |
Implementation Status |
|
Compile an inventory of hardware, software, and configurations |
◑ |
|
Identify the baseline network utilization and traffic growth predictions |
◑ |
|
Determine bandwidth allocation needs for variations and prioritize network traffic |
◑ |
|
Run simulations and perform analyses of network usage |
○ |
|
Make refinements to the network and continually monitor the health of the infrastructure |
◑ |
Legend: ● = addressed: The Coast Guard demonstrated that it had fully implemented the practice; ◑ = partially addressed: The Coast Guard demonstrated that it implemented some, but not all of the practice; and ○= not addressed: The Coast Guard could not demonstrate that it had implemented the practice.
Source: GAO analysis of U.S. Coast Guard documentation and industry publications. | GAO-22-105092
In accordance with the January 2017 agreement between the Department of Homeland Security and Department of Defense (DOD), the Coast Guard is to follow DOD's Risk Management Framework. This framework establishes two different cybersecurity risk management processes for identifying and applying cybersecurity controls for IT and for operational technology resources. However, the Coast Guard did not consistently apply the framework for its operational technology. This inconsistency is due in part to the lack of a comprehensive and accurate inventory. In addition, it lacks a cybersecurity risk management process for two types of operational technology—industrial control systems and supervisory control and data acquisition systems. Without a consistently applied process, accurate inventory, and coverage for all systems, the Coast Guard cannot ensure effective management of cybersecurity risks.
In March 2021, the Coast Guard issued a cloud strategy that outlines its strategic objectives for cloud computing over the next five years. The cloud strategy and associated relevant documentation incorporated most federal cloud requirements and guidance. However, the Coast Guard did not address key actions related to security and its workforce. Updating its strategy to include all cloud-related requirements and guidance would further facilitate the migration to cloud services.
Why GAO Did This Study
The U.S. Coast Guard, a component of the Department of Homeland Security, relies extensively on IT systems and services to carry out its 11 statutory missions. It also relies on operational technology, which encompasses a broad range of programmable systems or devices that interact with the physical environment, such as sensors and radar. Historically, the Coast Guard has had longstanding issues managing its technology resources. As such, it plans to spend $93 million to improve the reliability and performance of these resources in fiscal year 2022.
The William M. (Mac) Thornberry National Defense Authorization Act for Fiscal Year 2021 included a provision for GAO to review several aspects of the Coast Guard's IT program. This report addresses, among other things, the extent to which the Coast Guard (1) has a process to plan for network capacity; (2) has cybersecurity risk management processes for IT and for operational technology; and (3) has incorporated federal requirements in its strategy for cloud computing.
To do so, GAO evaluated the Coast Guard's IT policies and procedures against common practices for network capacity planning. GAO also analyzed the Coast Guard's cybersecurity processes for IT and operational technology and assessed their application. Further, it assessed the cloud strategy and other related documentation against federal requirements and guidance.
Recommendations
GAO is making eight recommendations to improve the Coast Guard's IT program implementation. The Department of Homeland Security agreed with all eight recommendations.
Recommendations for Executive Action
| Agency Affected | Recommendation | Status |
|---|---|---|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to develop network capacity planning policies and procedures that address the leading practices we identified, including (1) compiling a complete and accurate inventory of hardware, software, and configurations; (2) identifying traffic growth predictions; (3) prioritizing network traffic; (4) performing simulations and what-if-analyses; and (5) continually monitoring the health of the infrastructure to ensure it is meeting demand and mission needs. (Recommendation 1) |
In July 2024, the Coast Guard stated that it was initiating a comprehensive review to assess existing materials, identify areas needing new policies, and draft comprehensive procedures. The agency stated that this process will address areas where legacy policies are outdated or dedicated documentation was never developed. At that time, they anticipated that this action would be completed by the end of 2025. As of May 2026, we have not received an update from Coast Guard. We will continue to monitor Coast Guard's efforts to implement this recommendation.
|
| United States Coast Guard |
Priority Rec.
The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to implement the leading practices for network capacity planning that we identified, including (1) compiling a complete and accurate inventory of hardware, software, and configurations; (2) identifying traffic growth predictions; (3) prioritizing network traffic; (4) performing simulations and what-if-analyses; and (5) continually monitoring the health of the infrastructure to ensure it is meeting demand and mission needs. (Recommendation 2) |
In February 2025, the Coast Guard stated that through its Infrastructure Managed Services contract, awarded in December 2022, it has required that its vendor address the five leading practices in the recommendation. In April 2026, Coast Guard stated that all of the actions to address this recommendation were in progress and expected most of them to be completed by the end of fiscal year 2027. However, Coast Guard did not have an estimated time frame for completing the inventory of hardware, software, and configurations. To fully implement the recommendation, the Coast Guard will need to demonstrate that it has established and implemented policies and practices that address each of the leading practices we identified for network capacity planning. We will continue to monitor the Coast Guard's efforts to implement this recommendation.
|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to establish a comprehensive and accurate inventory of all operational technology, including ICS and SCADA systems. (Recommendation 3) |
According to DHS, the Coast Guard has efforts underway to consolidate its operational technology inventory data into a central, comprehensive inventory. In April 2026, the Coast Guard stated that it expected to have the inventory completed by September 30, 2029. We will continue to monitor the Coast Guard's efforts in implementing this recommendation.
|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to develop a plan or strategy for aligning all operational technology to the Department of Defense risk management framework, including time frames for completing the alignment. (Recommendation 4) |
In July 2025, the Coast Guard provided a corrective action plan that identified the steps to be taken to align all operational technology to the Department of Defense risk management framework. However, this plan did not include time frames. As of May 2026, Coast Guard has not provided an updated plan with time frames for each identified step. The Coast Guard stated that all steps in the plan should be completed by the end of 2029. We will continue to monitor the agency's progress in implementing this recommendation.
|
| United States Coast Guard |
Priority Rec.
The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to ensure that the plan or strategy for aligning all operational technology to the Department of Defense risk management framework is effectively implemented. (Recommendation 5) |
In February 2024, the Coast Guard updated its Cybersecurity Policy to require that all operational technology comply with the Department of Defense risk management framework. In July 2025, the Coast Guard provided a plan for aligning all operational technology to the Department of Defense risk management framework. As of May 2026, it estimated that the plan would be fully implemented by the end of 2029. To fully implement the recommendation, the Coast Guard will need to demonstrate that it has fully implemented its plan to align its operational technology to the Department of Defense's risk management framework. We will continue to monitor the agency's progress in implementing this recommendation.
|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to update existing policies and procedures to explicitly describe a cybersecurity risk management process for ICS and SCADA systems. (Recommendation 6) |
In February 2024, Coast Guard updated its cybersecurity policy to include requirements for ICS and SCADA systems to follow the DOD cybersecurity risk management process. As a result of this action, the Coast Guard is better positioned to ensure that it is effectively managing risks to those systems.
|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to send its list of cloud services that do not meet FedRAMP requirements to the appropriate agency head for submission to the Federal CIO. (Recommendation 7) |
In February 2025, the Coast Guard stated that the contract for their application rationalization effort that includes readiness to migrate to an approved commercial cloud, was extended to March 2025. As part of this effort, according to Coast Guard officials, a complete list of applications, both on premises and in the commercial cloud, will be generated and it will include anything that does not meet FedRAMP requirements. The officials added that a list of applications that are in scope will be provided after completion of the effort. As of May 2026, the Coast Guard had not provided a timeframe for completion. We will continue to monitor Coast Guard's efforts in implementing this recommendation.
|
| United States Coast Guard | The Commandant of the United States Coast Guard should direct the Deputy Commandant for Mission Support to update the service's cloud strategy and other relevant documentation to include a cross-walk of new and old skills and occupational categories, and to conduct a skills gap analysis. (Recommendation 8) |
In July 2025, the Coast Guard stated that a newly established Cloud Center of Excellence, pending Congressional funding, will be responsible for drafting an updated cloud strategy that will provide a plan to address and conduct the skills crosswalk, occupational categories, and skills gaps. As of May 2026, the Coast Guard anticipates that this action will be completed by the first quarter of fiscal year 2027. We will continue to monitor Coast Guard's efforts in implementing this recommendation.
|
