Internet-Connected Technologies Can Improve Services, but Face Risks of Cyberattacks
Our nation’s critical infrastructure includes sectors that provide essential services, such as electricity, health care, and transportation. These sectors increasingly rely on internet-connected technologies to support their mission and operation, such as the Internet of Things. However, this technology use also makes critical infrastructure vulnerable to cyberattacks—for example, the May 2021 ransomware cyberattack on an American oil pipeline system that led to regional gas shortages.
The federal government plays an important role in protecting this infrastructure from cyberattacks. Today’s WatchBlog post looks at the cybersecurity of internet-connected devices and our recent report on federal efforts to secure these devices.
Where are the potential vulnerabilities?
The use of Internet of Things (IoT) and operational technology (OT) creates points of entry that can leave critical infrastructure vulnerable to cyberattacks.
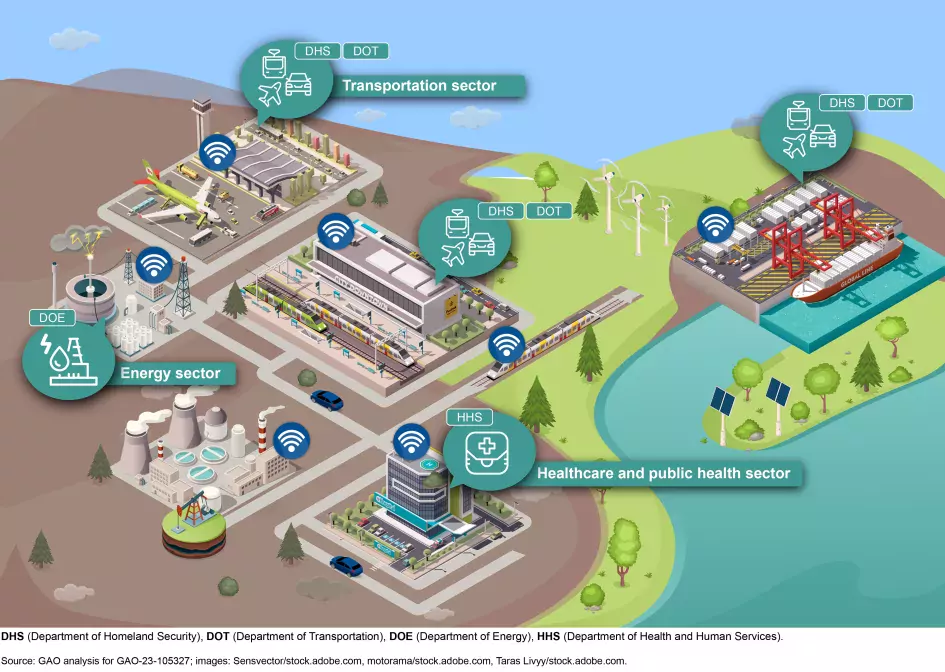
- Some examples of IoT in critical infrastructure include building access controls and badge readers, fuel usage or route monitoring, or applications like those advising passengers when the next bus or train is arriving. In health care, connected medical devices, like pacemakers and MRIs, are also part of the IoT.
- OT can be found in as varied environments as electricity generating stations and as part of the energy grids, on the production lines of medical device and pharmaceutical manufacturers, in ship-to-shore cranes, and in devices to control the speed of trains.
Depiction of Critical Infrastructure Sector Uses of Internet-Connected Devices
Image
IoT and OT devices and systems that support our nation’s critical infrastructure are inherently at risk. The risks include escalating and emerging threats from around the globe, new and more destructive attacks, and insider threats from witting or unwitting employees.
Cyber threats to IoT and OT can include purposeful attacks, environmental disruptions, and human/machine errors. These incidents may result in harm to the United States’ national and economic security interests.
For example, in July 2022, federal agencies that lead cybersecurity, law enforcement, and homeland security efforts warned health care entities (like hospitals) to lockdown devices that use IoT. This was in response to the threat from North Korean cyber attackers that sought to use IoT (among other entry points) to gain access to medical IT systems and holding medical information and data for ransom.
Federal efforts to mitigate IoT and OT cybersecurity risks
The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) and the National Institute of Science and Technology (NIST) have issued guidance and provided resources to help federal agencies and private entities manage cyber risks associated with internet-connected devices. In addition, each critical infrastructure sector has a lead agency responsible for assisting and protecting one or more of the nation’s 16 critical infrastructures, including supporting the security and resilience programs and associated activities of their designated sector. For example, the health care sector’s cybersecurity efforts are led by the Department of Health and Human Services.
For our December report, we met with agencies to see how they are assessing the effectiveness of their efforts. We found that they had not conducted risk assessments about their use of IoT and OT. Without conducting sector wide risk assessments, organizations will not know what additional security protections could be needed to address growing and evolving threats. We recommended that they conduct risk assessments that include IoT and OT.
The agencies responsible for providing leadership to our nation’s critical infrastructure sectors told us that the relationship between the private sector and government is voluntary. This, they said, makes it challenging to collect insight and measure their progress toward cybersecurity goals. But we think more could be achieved by these agencies and we recommended that these agencies address these gaps in their cybersecurity planning.
Find out more about our work on cybersecurity risks in IoT and OP, and federal efforts to address them by checking out our full report.
- Comments on GAO’s WatchBlog? Contact blog@gao.gov.
GAO Contacts
Related Products

GAO's mission is to provide Congress with fact-based, nonpartisan information that can help improve federal government performance and ensure accountability for the benefit of the American people. GAO launched its WatchBlog in January, 2014, as part of its continuing effort to reach its audiences—Congress and the American people—where they are currently looking for information.
The blog format allows GAO to provide a little more context about its work than it can offer on its other social media platforms. Posts will tie GAO work to current events and the news; show how GAO’s work is affecting agencies or legislation; highlight reports, testimonies, and issue areas where GAO does work; and provide information about GAO itself, among other things.
Please send any feedback on GAO's WatchBlog to blog@gao.gov.




