Critical Infrastructure Protection: CISA Should Improve Priority Setting, Stakeholder Involvement, and Threat Information Sharing
Fast Facts
The National Critical Infrastructure Prioritization Program is intended to identify the critical infrastructure assets in most need of protection.
Nearly all federal and state officials we spoke with questioned the program's relevance and usefulness. For example, they said it doesn't consider the most prevalent infrastructure threats, such as cyberattacks.
CISA (the agency running the program) has started shifting its focus from simply protecting a set of critical assets to improving the resilience of critical functions—e.g., supplying water. But, it could do more to communicate this shift.
Our recommendations address this and other issues.
Chemical Facility Storage Tanks
Highlights
What GAO Found
Through the National Critical Infrastructure Prioritization Program, the Cybersecurity and Infrastructure Security Agency (CISA) is to identify a list of systems and assets that, if destroyed or disrupted, would cause national or regional catastrophic effects. Consistent with the Implementing Recommendations of the 9/11 Commission Act of 2007, the program works to annually update and prioritize the list. The program's list is used to inform the awarding of preparedness grants to states. However, nine of 12 CISA officials and all 10 of the infrastructure stakeholders GAO interviewed questioned the relevance and usefulness of the program. For example, stakeholders identified cyberattacks as among the most prevalent threats they faced but said that the program's list was not reflective of this threat. Further, according to CISA data, since fiscal year 2017, no more than 14 states (of 56 states and territories) provided updates to the program in any given fiscal year. Ensuring that its process for determining priorities reflects current threats, such as cyberattacks, and incorporates input from additional states would give CISA greater assurance that it and stakeholders are focused on the highest priorities.
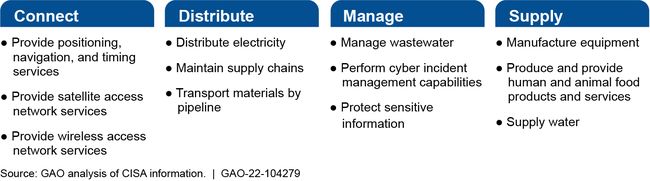
In 2019, CISA published a set of 55 critical functions of government and the private sector considered vital to the security, economy, and public health and safety of the nation. According to CISA officials, this new National Critical Functions framework is intended to better assess how failures in key systems, assets, components, and technologies may cascade across the 16 critical infrastructure sectors. Examples of critical functions are shown below in CISA's four broad categories of “connect” (nine of the 55 functions), “distribute” (nine), “manage” (24), and “supply” (13).
Examples of Cybersecurity and Infrastructure Security Agency (CISA) National Critical Functions
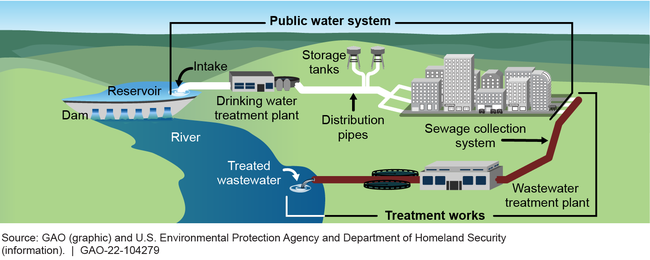
CISA is currently carrying out a process to break down each of the 55 national critical functions (such as “supply water”) into systems (such as “public water systems”) and assets (including infrastructure such as “water treatment plants”), as illustrated below.
Examples of Critical Infrastructure Systems and Assets That Support the National Critical Function “Supply Water”
CISA plans to integrate the National Critical Functions framework into broader prioritization and risk management efforts, and has already used it to inform key agency actions. For example, CISA used the framework to analyze the impact of COVID-19 on critical infrastructure. Although CISA initiated the functions framework in 2019, most of the federal and nonfederal critical infrastructure stakeholders that GAO interviewed reported being generally uninvolved with, unaware of, or not understanding the goals of the framework. Specifically, stakeholders did not understand how the framework related to prioritizing infrastructure, how it affected planning and operations, or where their particular organizations fell within it. In response, CISA officials stated that stakeholders with local operational responsibilities were the least likely to be familiar with the National Critical Functions, which were intended to improve the analysis and management of cross-sector and national risks. Still, CISA officials acknowledged the need to improve connection between the National Critical Functions framework and local and operational risk management activities and communications. In addition, CISA lacks an available documented framework plan with goals and strategies that describe what it intends to achieve and how. Without such a documented plan, stakeholders' questions regarding the framework will likely persist.
CISA offers physical and cybersecurity assessments to critical infrastructure partners, but the agency's 2020 reorganization resulted in challenges in communicating and coordinating the delivery of some cybersecurity services. According to regional staff, their ability to effectively coordinate the cybersecurity services that CISA headquarters delivered was impaired because of staff placement following the reorganization. Specifically, staff conducting outreach and offering a suite of cybersecurity assessments to critical infrastructure stakeholders are located in regional offices, while CISA offers additional cyber assessment services using staff from a different division—the Cybersecurity Division—which operates out of headquarters. Addressing these communication and coordination challenges can improve CISA's cybersecurity support.
CISA analyzes and shares threat information related to critical infrastructure; however, stakeholders reported needing more regionally specific information to address those threats. For instance, selected stakeholders that GAO spoke to said that CISA's threat information helped them to understand the broader threat landscape, such as threats to election security and COVID-19 response efforts. Almost half (12 of 25) of the stakeholders reported needing additional information related to the threats specific to their regions and local infrastructure. Specifically, stakeholders told us that organizations in their regions were primarily concerned with active shooters, chemical spills, or biological attacks and, thus, needed information that was applicable to those threats.
Why GAO Did This Study
The risk environment for critical infrastructure ranges from extreme weather events to physical and cybersecurity attacks. The majority of critical infrastructure is owned and operated by the private sector, making it vital that the federal government work with the private sector, along with state, local, tribal, and territorial partners. CISA is the lead federal agency responsible for overseeing domestic critical infrastructure protection efforts.
GAO was asked to review CISA's critical infrastructure prioritization activities. This report examines (1) the extent to which the National Critical Infrastructure Prioritization Program currently identifies and prioritizes nationally significant critical infrastructure, (2) CISA's development of the National Critical Functions framework, and (3) key services and information that CISA provides to mitigate critical infrastructure risks.
GAO analyzed agency documentation and conducted interviews with critical infrastructure stakeholders representing the energy, water and wastewater systems, critical manufacturing, and information technology sectors; six of 10 CISA regions; and six states to understand the need for any improvements to CISA's efforts, among other things. GAO selected these six states based on population size and the amounts of grant awards received from DHS's State Homeland Security Program.
Recommendations
GAO recommends that CISA take the following six actions and DHS concurred:
- improve its process for identifying critical infrastructure priorities to better reflect current threats;
- seek input from states that have not provided recent updates on identifying critical infrastructure;
- involve stakeholders in the development of the National Critical Functions framework;
- document goals and strategies for the National Critical Functions framework;
- improve efforts to coordinate cybersecurity services; and
- share regionally specific threat information.
Recommendations for Executive Action
| Agency Affected | Recommendation | Status |
|---|---|---|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should ensure that CISA's process for developing a prioritized list of critical infrastructure that would cause national or regional catastrophic effects if destroyed or disrupted reflects current threats. (Recommendation 1) |
As of March 2024, CISA took steps to ensure its process for developing a prioritized list of critical infrastructure reflects current threats and reported that its annual review process will help ensure that any future threat environment changes are appropriately reflected in the program's nomination process and thresholds. A National Critical Infrastructure Prioritization Program (NCIPP) nomination consists of three elements : (1) infrastructure of interest; (2) a scenario of interest, such as a terrorist act or natural disaster; and 3) disruption consequences, such as economic loss and fatalities. In August 2022, CISA reported developing a plan to review the NCIPP thresholds and criteria throughout fiscal year 2023. In March 2024, CISA reported that it completed its review of NCIPP's nomination thresholds and other aspects of the program and determined that the nomination thresholds were appropriate given the threat environment. CISA's fiscal year 2025 NCIPP nomination guidance details these thresholds, as well as a range of scenarios that critical infrastructure stakeholders can use to nominate assets or systems to the NCIPP list. CISA officials noted that the fiscal year 2025 guidance includes cyber-driven events as a nomination scenario, which allows critical infrastructure stakeholders to proactively identify, develop, and plan for cyber scenarios with the potential to negatively affect U.S. critical infrastructure. CISA's commitment to routinely reviewing the NCIPP thresholds and nomination process should help ensure that the program reflects current threats. CISA's actions therefore meet the intent of our recommendation.
|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should ensure that CISA's process for developing a prioritized list of critical infrastructure that would cause national or regional catastrophic effects if destroyed or disrupted includes input from additional states that have not provided recent nominations or updates. (Recommendation 2) |
In February 2022, CISA's National Risk Management Center (NRMC) reported that it will work with CISA Regional staff to make affirmative outreach to states who did not submit nominations to the National Critical Infrastructure Prioritization Program (NCIPP) in Fiscal Years 2019, 2020, or 2021 to ensure these states were aware of the program and the process to submit nominations. During the next nomination data call, CISA NRMC said it would also provide an option for states to affirm that no new assets currently on the NCIPP list have been taken offline. As part of the FY 2023 NCIPP data call, CISA NRMC reported emailing the data call kickoff memo and nomination materials to all states and territories through the DHS Office of Intergovernmental Affairs. In June 2022, through the FEMA Grants Programs Directorate, CISA NRMC distributed the nomination package and kickoff memo to all grant program stakeholders. Additionally, CISA NRMC hosted calls with CISA's stakeholder outreach staff to explain the importance of participation in the program. CISA also reported conducting several calls with state and regional partners to answer questions about the program. CISA reported that it will solicit feedback from states that do not participate to ask that these stakeholders suggest improvements to increase participation in future years. In November 2022, CISA finished updating its policies and procedures to help ensure responses from all program participants each year. These program updates should inform CISA's understanding of why some stakeholders may not be participating and will better position CISA to ensure it has as much current information from stakeholders as possible. These actions meet the intent of our recommendation.
|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should ensure that stakeholders are fully engaged in the implementation of the National Critical Functions framework. (Recommendation 3) |
CISA's National Risk Management Center has engaged with private sector and government partners to develop and apply the National Critical Functions (NCF) framework, and CISA reported in February 2022 that it is committed to continuing, improving, and expanding its engagement with stakeholders. For example, to engage with stakeholders, CISA has used webinars, meetings with sector councils and cross-sector councils, workshops, and meetings with individual public and private entities. In March 2021, CISA established the Federal Risk Management Working Group through the Federal Senior Leadership Council, which ensures federal partners, including Sector Risk Management Agencies, have a formal role in implementing the NCF framework. CISA reported that it developed 55 stakeholder linkage profiles for each NCF to ensure it understands the full range of stakeholders involved in addressing and supporting each function. CISA reported that, as of November 2022, it is using these stakeholder linkage profiles to form communities of interest for each NCF to provide input into framework development and support risk management activities. CISA also reported that its outreach and coordination efforts remained ongoing, including the Federal Risk Management Working Group. CISA's efforts to engage and coordinate with its stakeholders are varied, and the National Risk Management Center's team has established the necessary channels and mechanisms to ensure that stakeholders are engaged in implementing the NCF framework. Accordingly, CISA's actions have fulfilled the intent of our recommendation.
|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should document, as appropriate, goals and strategies for the National Critical Functions framework. (Recommendation 4) |
As of July 2025, CISA officials reported that they are evaluating the National Critical Functions framework goals and strategies to determine consistency with Executive Order 14239 requirements. The Executive Order requires that DHS propose changes to various policies, including the National Critical Functions, to ensure state and local governments and individuals have improved communications with Federal officials and a better understanding of federal roles. CISA officials reported that they are coordinating within DHS and with the National Security Council on implementing this requirement. We will continue to monitor CISA's efforts and update the status of this recommendation accordingly.
|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should implement processes to improve communication and coordination between critical infrastructure organizations and CISA headquarters and regional staff. (Recommendation 5) |
In June 2023, CISA's Integrated Operations Division (IOD) implemented its Service Delivery Change Request tool. CISA officials stated that this tool provides a more effective mechanism for CISA Regional personnel and critical infrastructure stakeholders to request changes to existing CISA products and services, as well as to request a new product or service. CISA's guidance for implementing the tool acknowledges that CISA's service delivery model to stakeholders results in many services designed by headquarters officials but implemented by CISA's field personnel. The tool is intended to facilitate a continuous feedback loop between these entities to improve communication and coordination. CISA's implementation of the Service Delivery Change Request tool standardizes information flow among CISA headquarters and regional staff in their efforts to provide services to critical infrastructure organizations, thereby addressing the intent of our recommendation.
|
| Cybersecurity and Infrastructure Security Agency | The Director of CISA should coordinate with relevant regionally based, federal, and nonfederal partners to regularly develop and distribute regionally specific threat information to each of CISA's 10 regions. (Recommendation 6) |
CISA officials reported in August 2022 that in response to our recommendation CISA's Intelligence sub-division established a Regional Engagement Lead whose primary purpose was to build and maintain threat information sharing relationships across CISA's 10 regions. As of October 2023, CISA's outreach and engagements with the regions had increased in frequency, according to CISA officials, and CISA determined a single employee serving as the regional engagement lead would not satisfy the engagement requirements being sought or provided to the regions. CISA then designated multiple members of CISA's Intelligence sub-division with a role in regional engagement activities. These staff members provided virtual threat briefings and regularly travel to the regions to provide classified and unclassified threat information, participate in tabletop exercises and other projects, as described by CISA officials and reflected in agency documentation. CISA's enhanced efforts to distribute threat information to CISA's regions address the intent of our recommendation.
|
