DOD Installations: Monitoring Use of Physical Access Control Systems Could Reduce Risks to Personnel and Assets
Fast Facts
In November 2009, an Army officer shot 45 people at Fort Hood, Texas. Four years later, a Navy contractor shot 16 people at the Navy Yard in Washington, D.C.
DOD increasingly uses physical access control systems to screen people who want to enter military installations. The systems scan credentials and check them against FBI and other government databases. However, we found that DOD didn't know the extent to which its installations were using these systems because the Army, Navy, and Marine Corps have not monitored their use.
We recommended that DOD monitor the use of these systems and resolve technical issues to improve their performance.
A service member checks a stopped car at the main gate on McConnell Air Force Base, Kansas.

A person in a military uniform checks a car stopped at a checkpoint.
Highlights
What GAO Found
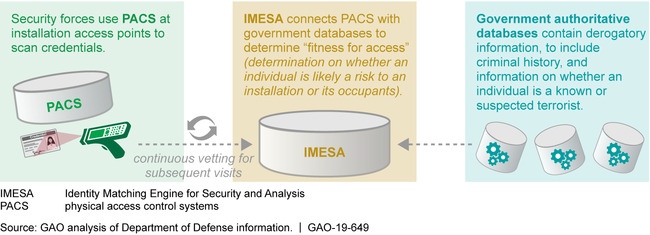
The Department of Defense (DOD) has issued guidance on accessing its domestic installations and strengthening physical access control systems (PACS)—used to scan credentials to authenticate the identity and authorize individuals to access DOD installations. Specifically, DOD has recently issued guidance directing the fielding of PACS and has fielded or plans to field such systems at domestic installations. The Defense Manpower Data Center (DMDC) developed the PACS used by the Air Force, the Navy, the Marine Corps, and the Defense Logistics Agency. The Army developed its own PACS. Both types of PACS electronically connect to DOD's Identity Matching Engine for Security and Analysis (IMESA). IMESA accesses authoritative government databases to determine an individual's fitness for access (i.e., whether an individual is likely a risk to an installation or its occupants), and continually vets this fitness for subsequent visits (see fig.).
PACS Connect to IMESA to Validate the Identity of Individuals and Continuously Vet Their Fitness for Access to Department of Defense Installations
The Air Force and DLA have monitored their installations' use of PACS, but the Army, the Navy, and the Marine Corps have not. Army, Navy, and Marine Corps installation officials stated that they do not monitor PACS use at their installations because there is no requirement to do so. Because the Army, the Navy, and the Marine Corps do not monitor PACS use and DOD does not require that they do so, those military services do not have the data they need to evaluate the effectiveness of PACS and make informed risk-based decisions to safeguard personnel and mission-critical, high-value installation assets. DOD, Army, Navy, and Marine Corps officials agreed that monitoring installations' use of PACS would be beneficial and could be readily accomplished without significant cost using existing technology.
The Army and DMDC have used a tiered approach and established helpdesks to address PACS technical issues. The Army has established performance measures and goals to assess its approach, which has improved the ability to resolve technical issues. DMDC, however, does not have performance measures and goals, and thus lacks the information needed to evaluate its PACS' performance and address issues negatively affecting operational availability.
Why GAO Did This Study
In November 2009, an Army officer killed or wounded 45 people at Fort Hood, Texas; 4 years later in September 2013, a Navy contractor killed or wounded 16 people at the Washington Navy Yard in Washington, D.C. Independent reviews conducted in the aftermath of these shootings identified physical access control weaknesses at DOD installations.
The conference report accompanying the National Defense Authorization Act for Fiscal Year 2018 contained a provision for GAO to assess DOD's installation access control efforts. GAO (1) described actions DOD has taken to develop guidance on physical access to domestic installations and to field PACS at these installations, (2) evaluated the extent to which DOD has monitored the use of fielded PACS at these installations, and (3) evaluated the extent to which DOD has implemented an approach for addressing PACS technical issues and assessing associated performance. GAO analyzed DOD guidance on physical access control requirements, and visited installations to discuss with installation command and security force officials their experiences using PACS. This is a public version of a sensitive report that GAO issued in May 2019. Information that DOD deemed sensitive has been omitted.
Recommendations
GAO made five recommendations, including that DOD monitor installations' use of PACS and develop appropriate performance measures and goals for resolving technical issues to improve PACS performance. DOD concurred with GAO's recommendations.
Recommendations for Executive Action
| Agency Affected | Recommendation | Status |
|---|---|---|
| Department of Defense | The Secretary of Defense should ensure that the Under Secretary of Defense for Intelligence requires that DOD components (including the military departments and the Defense Logistics Agency) monitor the use of PACS at their installations. (Recommendation 1) |
DOD concurred with this recommendation and identified actions that it was taking to implement this recommendation. Specifically, DOD is drafting a new volume of DODM 5200.08, Volume 1, Physical Security Program: Rules, Regulations, and Requirements that will require DOD Components with installation access control responsibility to monitor the use of their physical access control systems (PACS) at their installations. As of May 2022, DOD expects to issue the new manual in December 2025. As a result of delays in issuing Volume 1, OUSD(I&S) signed a memorandum on April 18, 2022, that authorizes Component-level access to PACS data, including PACS usage data, to enable the Components to monitor PACS usage. The actions taken by DOD meet the intent of our recommendation.
|
| Department of the Army | The Secretary of the Army should ensure that the Office of Provost Marshal General monitors the use of PACS at Army installations. (Recommendation 2) |
DOD concurred with this recommendation and identified actions that the Army was taking or planned to take to implement this recommendation. The Army expects to incorporate this recommendation into guidance by the end of 2025. The guidance will direct the Army Office of Provost Marshal General to monitor the use of PACS at Army installations through monthly reporting of PACS card scans. in the interim, while the guidance has been in the development and approval process, the Army has already begun collecting data on the numbers of PACS card scans at 98 CONUS installations.
|
| Department of the Navy | The Secretary of the Navy should ensure that the Commander, Navy Installations Command, monitors the use of PACS at Navy installations. (Recommendation 3) |
In response to our recommendation, the Department of the Navy revised SecNavInst 5500.35, which mandates the Services' (Navy and Marine Corps) use physical access control systems (PACS) to the maximum extent possible and requires that each Service monitor the use of their PACS. SecNav (DUSN) monitors the use of PACS by requiring the Services to provide monthly reporting of PACS statistics on a recurring basis. SecNavinst 5500.35 was issued on February 22, 2022. The actions taken by Navy meets the intent of our recommendation.
|
| Department of the Navy | The Secretary of the Navy, in coordination with the Commandant of the Marine Corps, should ensure that the Commander, Marine Corps Installations Command, monitors the use of PACS at Marine Corps installations. (Recommendation 4) |
In response to our recommendation, the Department of the Navy revised SecNavInst 5500.35, which mandates the Services' (Navy and Marine Corps) use of physical access control systems (PACS) to the maximum extent possible and requires that each Service monitor the use of their PACS. SecNav (DUSN) monitors the use of PACS by requiring the Services to provide monthly reporting of PACS statistics on a recurring basis. The revision of SecNavInst 5500.35 was issued on February 22, 2022. The actions taken by Navy meet the intent of our recommendation.
|
| Department of Defense | The Secretary of Defense should ensure that the Under Secretary of Defense for Personnel and Readiness develops appropriate performance measures and associated goals for the timely resolution of the Defense Biometric Identification System technical issues to facilitate improved PACS performance. (Recommendation 5) |
DOD concurred with this recommendation and identified actions that USD(P&R) and the Defense Manpower Data Center (DMDC) was taking or planned to take to implement this recommendation. DMDC performed a comprehensive assessment of performance measures and developed acceptable quality levels (AQL) of service and performance for the help desk and technical solutions. The enhanced AQLs have improved the timely resolution of DBIDS technical issues to facilitate improved PACS performance. DMDC developed a technical solution based on these enhanced AQLs to monitor help desk performance called ServiceNow. ServiceNow has the capability to support requirements and is being incorporated across the enterprise to improve performance, however, the procurement of certain modules will not be completed until the end of September 2026.
|
