An Ongoing Risk: Cybersecurity Attacks at Federal Agencies
Similar to how new flu shots come out each year to combat new strains of the virus, agencies must routinely adapt their cybersecurity efforts to address evolving threats.
In today’s WatchBlog, we look at the federal government’s approach to and strategy for securing its systems.
Read on and listen to our podcast with Greg Wilshusen, a director in our Information Technology and Cybersecurity team, to learn about what has been done and what needs to be improved.
Many attacks still occur
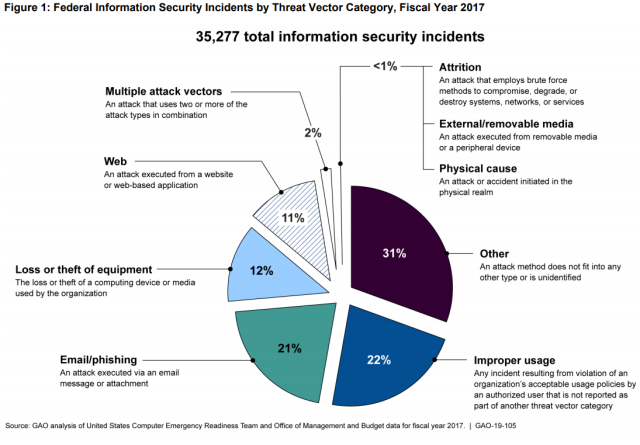
While federal agencies have gotten better at preventing and detecting intrusions into their systems, they are still vulnerable to attacks such as unauthorized computer invasions. In FY 2017, for instance, federal agencies reported more than 35,000 cybersecurity incidents.
Why is federal cybersecurity important?
When you step back to think about the vast amount of sensitive information the government maintains, it becomes apparent why cyberattacks pose a serious threat to our economic, national, and personal privacy and security. For example:
- The IRS keeps information about your income, marriage status, and other personal and financial information.
- The Centers for Medicare & Medicaid Services collect sensitive health information.
Are federal agencies working to improve security?
In some respects, agencies are doing a better job at protecting against cyberattacks than before the 2015 Office of Personnel Management data breach.
However, most agencies still don’t have an effective approach to securing their systems. For example, inspectors general at 17 of the agencies we reviewed in our recent report said that their information security programs weren’t effective enough.
What more can be done?
We’ve made more than 3,000 recommendations to agencies since 2010 related to cybersecurity shortcomings. Although many of these recommendations have been addressed, approximately 600 had not been implemented as of March 2019.
We recently recommended that DHS and the Office of Management and Budget help agencies improve their intrusion detection and prevention capabilities by, among other things, identifying what obstacles and impediments affect their ability to detect and prevent intrusions.
We also have plans to further assess the adequacy and effectiveness of federal agencies’ information security programs.
To learn more, read our full report.
-
- Questions on the content of this post? Contact Gregory C. Wilshusen at wilshuseng@gao.gov.
- Comments on GAO’s WatchBlog? Contact blog@gao.gov.
GAO Contacts
Related Products

GAO's mission is to provide Congress with fact-based, nonpartisan information that can help improve federal government performance and ensure accountability for the benefit of the American people. GAO launched its WatchBlog in January, 2014, as part of its continuing effort to reach its audiences—Congress and the American people—where they are currently looking for information.
The blog format allows GAO to provide a little more context about its work than it can offer on its other social media platforms. Posts will tie GAO work to current events and the news; show how GAO’s work is affecting agencies or legislation; highlight reports, testimonies, and issue areas where GAO does work; and provide information about GAO itself, among other things.
Please send any feedback on GAO's WatchBlog to blog@gao.gov.