Watching Out for Federal Cybersecurity
 Excerpted from GAO-13-187
Excerpted from GAO-13-187
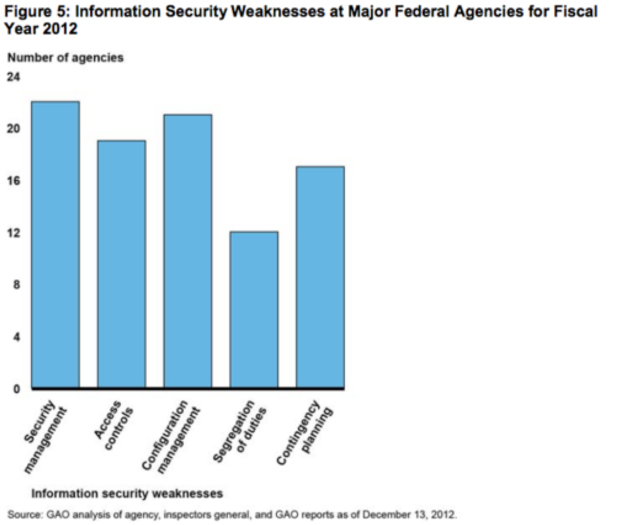
- limiting, preventing, and detecting inappropriate access to computer resources;
- planning for continuity of operations in the event of a disaster or disruption; and
- implementing information security management programs.
Excerpted from GAO-13-283
Other gaps in cybersecurity that we have identified include:- Information technology supply chain issues at the Departments of Energy, Homeland Security, Justice, and Defense;
- Security control weaknesses in the Environmental Protection Agency’s information systems; and
- Management and other security control issues with the Federal Communications Commission’s network security project.
- Documenting risk levels and the number of affected individuals for data breaches;
- Offering credit monitoring to affected individuals;
- Documenting lessons learned from breach responses;
- Testing incident response capabilities; and
- Developing or clarifying policies, plans, and procedures for incident response.
- Questions about the content of this post? Contact Greg Wilshusen at wilshuseng@gao.gov.
- Comments on the GAO WatchBlog? Contact blog@gao.gov.

GAO's mission is to provide Congress with fact-based, nonpartisan information that can help improve federal government performance and ensure accountability for the benefit of the American people. GAO launched its WatchBlog in January, 2014, as part of its continuing effort to reach its audiences—Congress and the American people—where they are currently looking for information.
The blog format allows GAO to provide a little more context about its work than it can offer on its other social media platforms. Posts will tie GAO work to current events and the news; show how GAO’s work is affecting agencies or legislation; highlight reports, testimonies, and issue areas where GAO does work; and provide information about GAO itself, among other things.
Please send any feedback on GAO's WatchBlog to blog@gao.gov.